news
Users of Windows need to be notified ASAP of a new ransomware strain and take immediate measures to patch.
Specifically, on May 12, 2017 a new strain of the Ransom.CryptXXX (WannaCry) strain of ransomware began spreading widely impacting a large number of organizations, particularly in Europe.
Wcry is demanding a ransom of $300 to $600 in Bitcoin to be paid by May 15, or, in the event that deadline is missed, a higher fee by May 19. The messages left on the screen say files will remain encrypted. It's not yet clear if there are flaws in the encryption scheme that might allow the victims to restore the files without paying the ransom.
If you have yet to install the Microsoft fix—MS17-010— you should do so immediately. You should also be extremely suspicious of all e-mails you receive, particularly those that ask the recipient to open attached documents or click on Web links.
If you have seen nonstandard activity and believe your customers’ information may have been exposed, please contact support.
Office 365 updates
To see all the office updates go to What’s new in Office 365
Here are some specific SharePoint Updates. If you are not using SharePoint, you are missing out on a major chunk of Office 365.
|
||||||
|
Contact us today to find out how to ensure you are up to date with Office365 new features and tools
Tim is now an Evernote Certified Consultant
 Late last year Tim completed the certification process to be called an Evernote Certified Consultant.
Late last year Tim completed the certification process to be called an Evernote Certified Consultant.
Now we can help you build out productivity solutions in Evernote for yourself or your team or your entire business.
Evernote is an awesome note taking app that syncs across devices and platforms, iOS, Android, Windows and Mac as well as in the browser.
Here are some of the productivity tips and information from recent Evernote Blogs and articles.
Do vs. Done Lists: Jot Down Your Small Wins to Amplify Success
7 Tips from Experts: Watch Business Productivity Soar in Evernote
Contact us to discuss how Evernote could be used in your business
This Week’s Productivity Tips
Here are some recently located productivity tips.
5 Dreadful email mistakes to avoid
One click. That’s all it takes. ![]() The Office Online extension adds a clickable icon to your Google Chrome™ browser, which allows you to open or create Office files and save them to OneDrive. After a one-time sign-in, one click is all you’ll need to unlock the power of Office.
The Office Online extension adds a clickable icon to your Google Chrome™ browser, which allows you to open or create Office files and save them to OneDrive. After a one-time sign-in, one click is all you’ll need to unlock the power of Office.
Get an online presentation built in just a few minutes using QuickStarter in Sway. Office 365 users – this tool is free in your online portal and allows you to create polished online company presentations in just a few minutes. No more agonising about web development costs. Just create and share to your customers.
7 Email tips to control your inbox
Get control of your inbox with these built-in features. If inbox management is something you struggle with then we can come and show you how to save time every day in shortcuts and other power tools that speed up your message management.
Check out a previous article that showcases some the best Outlook apps.
|
Office Extra | Your source for the newest ways to help you do more |
||||||
|
Collaboration is the key to success. That’s why Office 365 provides apps and services to help groups of all sizes and styles achieve together. And now, for high-velocity teamwork, there’s Microsoft Teams. Teams is the new chat-based workspace activated by over 30,000 organisations since it rolled out last November. It’s free with your subscription and ready to go. |
||||||
|
|
||||||
|
Also new from Office 365 |
||||||
|
As a subscriber, you get the latest upgrades like these and more. |
||||||
|
||||||
|
||||||
|
||||||
|
Contact us today to find out how to ensure you are up to date with Office365 new features and tools
On 14 September 2016, pursuant to the agreement of the House of Representatives and the Senate, a Joint Standing Committee was established to inquire into and report on the rollout of the National Broadband Network (NBN).
The committee is composed of nine Members and eight Senators.
The closing date for submissions is 31 March 2017.
Committee Secretariat contact:
PO Box 6100
Parliament House
Canberra ACT 2600
Phone: 02 6277 3585
Fax: 02 6277 5794
If any of our customers wants to make a submission about the current NBN rollout debacle please contact me as we can do a joint submission if you like.
There is also a public hearing in Redcliffe for those businesses local to the Moreton Bay Region.
Date: Thursday 6th April
Venue: Mon Komo Hotel, 99 Marine Parade, Redcliffe
Time: 9am – 3pm
The public forum is open for anyone to attend.
Contact us today to find out how to utilise these tools
Is Digital Transformation Just Hype?
Digital Transformation is one of the biggest (and most misused) business buzzwords right now.
What many people and businesses don’t realise is that it relies heavily on two underlying stages, of digital competence and digital usage before it can happen.
In other words, a business cannot achieve any of the expected gains from Digital Transformation if they haven’t changed their underlying understanding and usage of the digital technologies that are available to them.
Yes – this means CHANGING THE WAY YOU DO BUSINESS. Without changing there is no transformation.
Most likely you are using some digital technologies in your business, Office 365, Email, mobile technologies and so on. But if your business hasn’t changed how it does things then you are missing out on the amazing benefits these technologies can provide when used the way they were designed.
Here is a short checklist: If you answer Yes to any of these then you have not fully understood what business transformations are available to your business.
- Do you send emails with files attached?
- Do you have meetings where people bring pads and paper and take notes?
- Do you cancel / postpone meetings because an important person can’t be there physically?
- Do you still have a computer server on your premises?
- Do you keep your accounting records on a computer in your office? (E.g. MYOB etc.)
Here are some questions that if you answer No to you may be missing out on technology that is readily available, and likely being used by your competitors to gain an edge over you.
Do you have mobile EFTPOS and or mobile Sales Terminals?
- Can you readily access your files on your phone or tablet? E.g. that sales quote you just prepared. (And not because you emailed it to yourself as an attachment )
- Can you employ a new person and have them accessing email and data within an hour of being employed?
- If a machine breaks down in your factory do you get an automatic alert on your phone immediately?
- If negative feedback on social media happens, do you have a staff member who is notified immediately and deals with it to create a positive outcome?
There are many more tests of digital transformation. I suggest if you failed any of these tests above that you contact us for a discussion. Your competitors probably will.
We can also run a personalised workshop for you and your business for a flat rate of $175.
Contact us to discuss what digital transformation can do for your business
Moreton Technology Alliance – 2017 Digital Trends Function
For those in the Moreton Bay Region we warmly invite you to our next Moreton Technology Alliance function. Come along on Thursday night 20th April to have a drink and listen to the two Moreton Bay Digital Community Champions, Kate vanderVoort and James Novak, talk about the current trends in Social Media and 3D printing as they apply to business.
For all the event details and tickets ($15 includes 1 free drink) go to the MTA website
Follow Us On Social Media
As always Jethro is your web, cloud and technology specialists. I am constantly learning new things and spending time researching, playing and testing new systems and reading about other people in the IT world doing the same thing. If you want to follow along with what I share in various spaces, then connect with me:
- Twitter https://twitter.com/spyjournal technology, cycling, social media, management, business, and web
- LinkedIn http://www.linkedin.com/in/jethromanagement
- Delicious https://delicious.com/jethrocon saved links
- Blog http://spyjournal.biz all sorts of stuff including personal and family updates
- Spyjournal Facebook https://www.facebook.com/spyjournal.biz tech, cycling, and other stuff
- Subscribe to our daily Newspaper https://paper.li/spyjournal/1345852972
- Subscribe to our weekly Newspaper https://paper.li/spyjournal/1345853288
- Jethro Management Facebook https://www.facebook.com/JethroManagement business, management, web
- Jethro Marketing Facebook https://www.facebook.com/JethroMarketing social media, marketing
- Dreamcoat Photography Facebook https://www.facebook.com/DreamcoatPhotography
- Dreamsport Photography Facebook https://www.facebook.com/DreamSportPhotography
- Red Hot Snapper Facebook https://www.facebook.com/redhotsnapper roller derby
All content © Tim Miller. Feel free to share or send these emails on. If you want to unsubscribe just reply with Unsubscribe in the subject.
Inspired by a quick Skype for Business presentation I just did with three customers assisting them share their calendars I decided to write this short training tool. Outlook is the primary email management tool for most business people worldwide. It is also an extremely feature rich time management tool with many capabilities that a lot of people have no idea it can do.
 Here’s a short list of some of the amazing things you can do in Outlook, and particularly in Calendars.
Here’s a short list of some of the amazing things you can do in Outlook, and particularly in Calendars.
- Out of Office messages (technically not in the calendar) - utilising dates and time to send out of messages to either or both internal and external email recipients.
- Delegate permissions – sharing your calendar with others in your organisation to see or edit calendar items on your behalf.
- View multiple calendars – see multiple people’s calendars stacked side by side, on top or even overlaid to see calendars and find joint free time.
- View and subscribe to external calendars – see others calendars or appointments.
- Share your calendar externally – free busy time, free busy with subject and location, or all calendar information.
- Use categories and colours for quick visual calendar – see the image.
- Plugins (Tools from the Office Store) Find time is possibly the best tool ever – and its free! https://findtime.microsoft.com/
- Create Skype for Business meeting requests right inside Outlook Calendar items by clicking the Skype icon on the toolbar.
Contact us today to find out how to utilise these tools
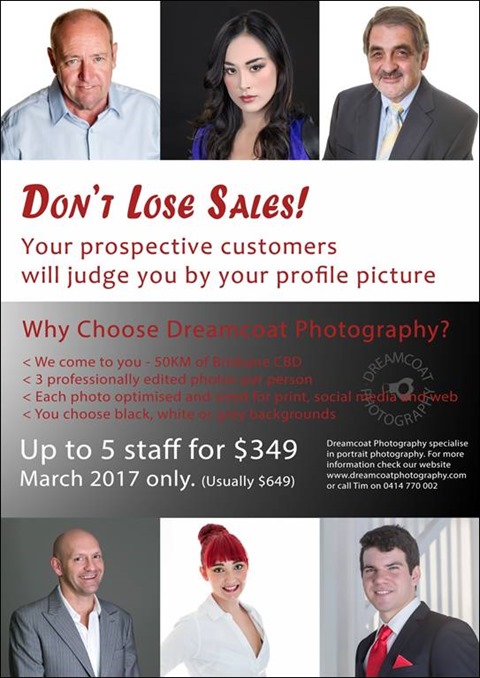
Improve Your Marketing with the Right Corporate Image
Your sales begin with you. Your corporate profile on your website and LinkedIn either attracts people to do business with you or drives them away. Even worse is having a grey shadow head.
We have this great offer for March 2017 with a discounted headshot price for up to 5 staff.
Contact us today to book your photoshoot
Follow Us On Social Media
As always Jethro is your web, cloud and technology specialists. I am constantly learning new things and spending time researching, playing and testing new systems and reading about other people in the IT world doing the same thing. If you want to follow along with what I share in various spaces, then connect with me:
- Twitter https://twitter.com/spyjournal technology, cycling, social media, management, business, and web
- LinkedIn http://www.linkedin.com/in/jethromanagement
- Delicious https://delicious.com/jethrocon saved links
- Blog http://spyjournal.biz all sorts of stuff including personal and family updates
- Spyjournal Facebook https://www.facebook.com/spyjournal.biz tech, cycling, and other stuff
- Subscribe to our daily Newspaper https://paper.li/spyjournal/1345852972
- Subscribe to our weekly Newspaper https://paper.li/spyjournal/1345853288
- Jethro Management Facebook https://www.facebook.com/JethroManagement business, management, web
- Jethro Marketing Facebook https://www.facebook.com/JethroMarketing social media, marketing
- Dreamcoat Photography Facebook https://www.facebook.com/DreamcoatPhotography
- Dreamsport Photography Facebook https://www.facebook.com/DreamSportPhotography
- Red Hot Snapper Facebook https://www.facebook.com/redhotsnapper roller derby
All content © Tim Miller. Feel free to share or send these emails on. If you want to unsubscribe just reply with Unsubscribe in the subject.








![clip_image010[1] clip_image010[1]](http://www.jethroconsultants.com/files/clip_image0101.jpg)